Blog
The Modern Application Model
Most of today’s software development is occurring within the Application Layer as defined by the OSI Model. However that definition is a bit dated and does not exactly reflect today’s technology. We need a new model to visualize what we, Application Software Developers, are building.

The New Normal — Scaling the challenges of a Modern CTO
Whether you’re a Founding CTO or an Enterprise CTO, you cannot go at it alone. You have to hire a team around you to help delegate and distribute a modern CTO’s responsibilities and overlapping technical domains, such as CIO, CDO, CMO, etc.
Challenges of a Modern CTO
A CTO needs to be able to operate and be experienced in many areas beyond just the tactical. To be successful, they require Technical & People Leadership experience.

Solving Solved Problems — Lessons from my journey
How seemingly “solved problems” in technology keep repeating themselves, and how developers keep falling into the trap of reinventing the wheel

So long, and thanks for all the packages!
Announcing my departure from npm

Ultimate Guide to Non-Rectangular Headers
Non-Rectangular Headers have recently been taken over the web. This “new” design trend seems simple and straightforward at first, but can be a little tricky to accomplish.
Alarm.com Camera Vulnerability
Alarm.com uses a Java web player to live-stream video from your home security cameras to your browser, the Java player source code is easily decompiled and can grant an attacker access to the camera and home network.

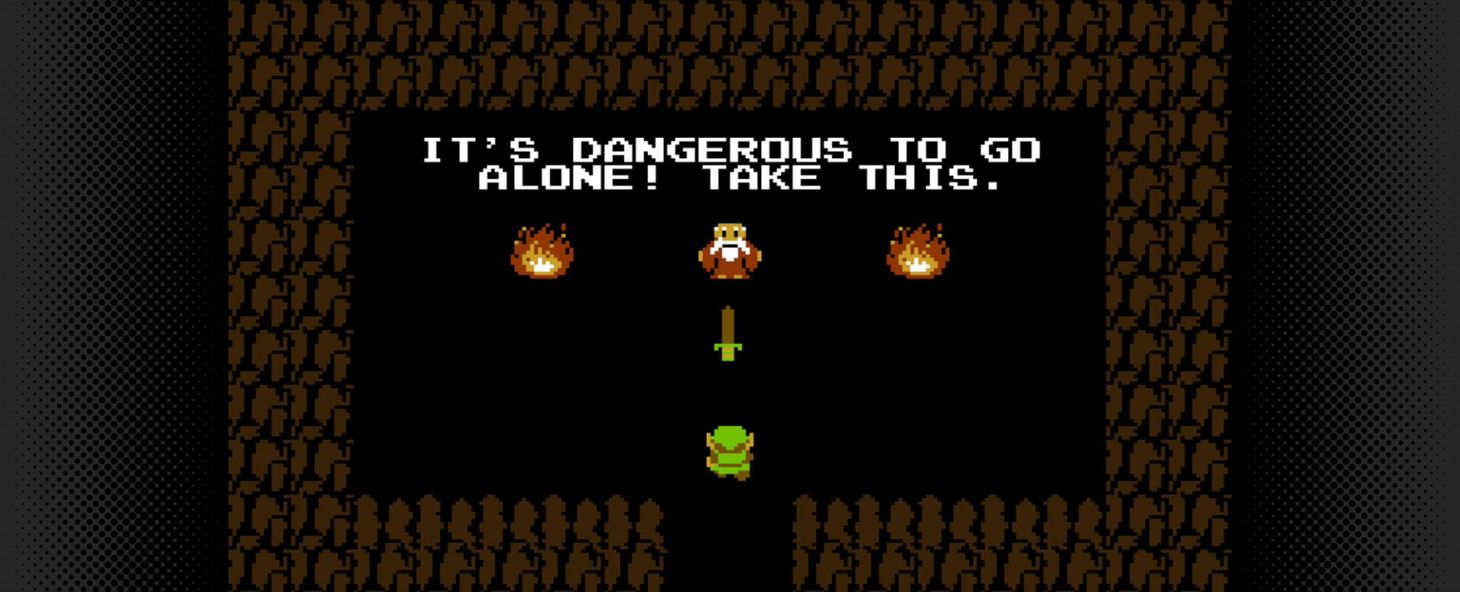
Burn the Ships!
A startup leadership lesson from the 7th century

Battle Scars
Professional Growth & Experience through time and knowledge in the workplace trenches

Github GPG + Keybase PGP
Using Keybase.io PGP Keys for GPG signature verification on Github can be a bit tricky. Luckily, you can still use your Keybase.io on Github with a simple workaround, following these instructions

